
Start Building with MultiversX
Build the future, today.
Create the next generation of Web3 applications.
Now is our time. There are no shortcuts, and no excuses.

Inside the Internet-Scale blockchain
Building on the most robust Web3 infrastructure has never been easier.
Learn how it works
The technology that powers innovation
The possibilities are endless, and the future is yours to build.
MultiversX Docs
Payments become viable on a blockchain when the foundational layer can handle the billions of unbanked plus the billions already banked.
Scaling is a must, it is not optional.
Robert Sasu
Core Developer, MultiversX

Builder Resources
Whether you’re new to Web3, new to MultiversX, or a seasoned builder, you can still upgrade your skills.
Docs
Documentation and guides on getting started with MultiversX.
MultiversX Smart Contract Framework
The most complete smart contract framework on MultiversX.
MultiversX Virtual Machine
WASM-based Virtual Machine for running MultiversX Smart Contracts.
Integrate MultiversX
Guides on how to integrate the MultiversX network in your app.
Become a Validator
Become a node operator to secure the chain, earn rewards.
Community Resources
Smart contracts, SDKs, dev libraries, articles, tutorials, and all other dev stuff.

At MultiversX, builders are heroes.
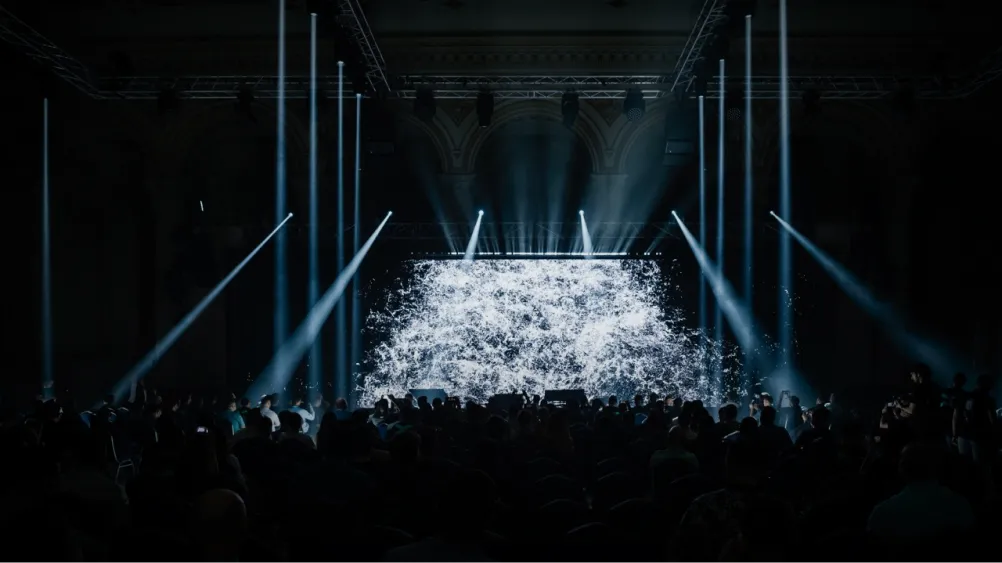
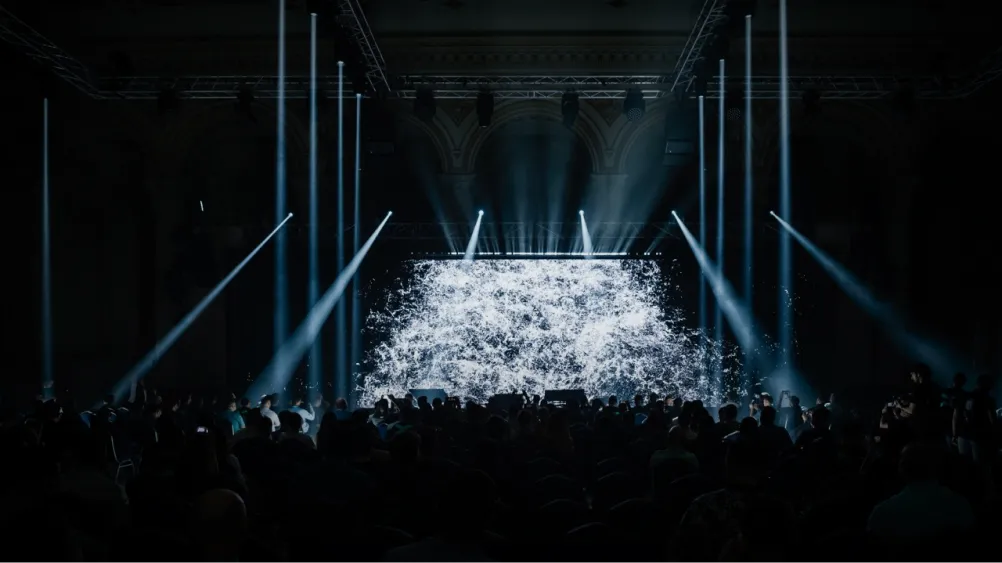
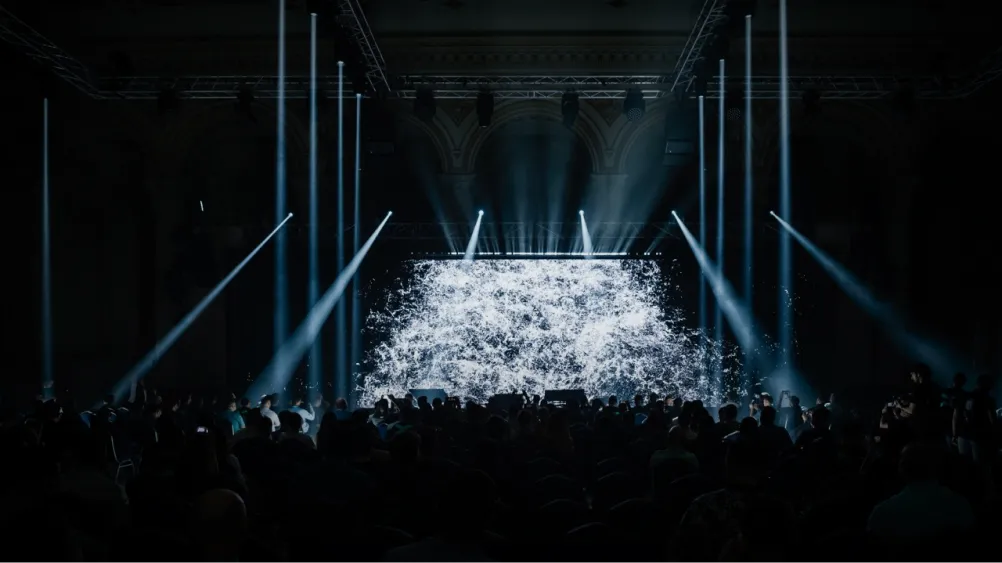
Recap of xDay /hackathon

Feeling Stuck?
Are you stuck on a problem or just want to share your successes? Join highly driven individuals such as yourself.
Never miss an update
They’ll be worth it. We constantly make significant improvements to the protocol, API, and developer tooling.
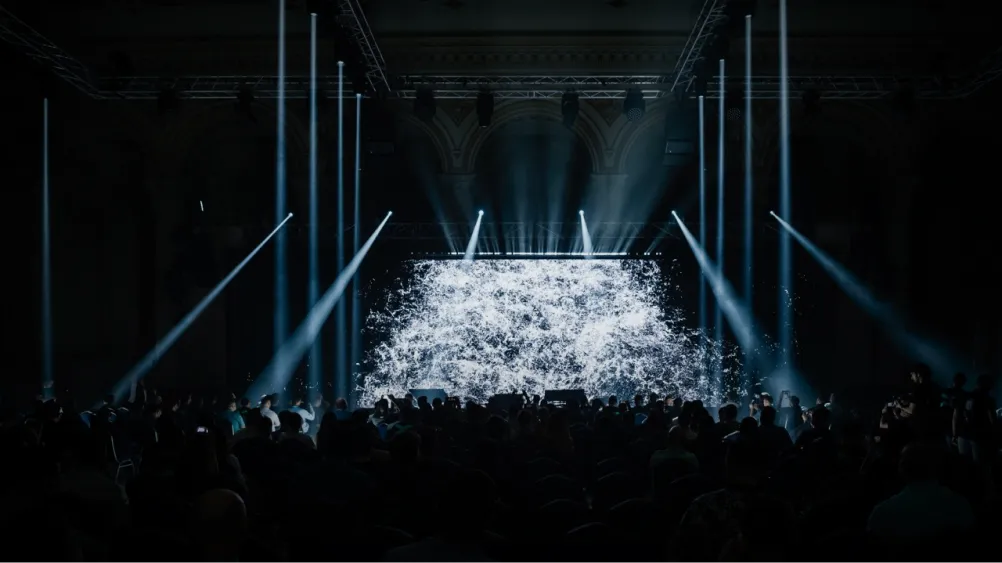



2,6k
xDay 2023 attendees








2,6k
xDay 2023 attendees










39k
On Discord and Telegram
1k+
participants in the xDay 2023 hackathon







39k
On Discord and Telegram
1k+
participants in the xDay 2023 hackathon


Alone, we can do so little,
together, we can move mountains.